When working with Windows and 3rd party applications, it can be difficult to stay on top of all vulnerabilities that could lead to potential security issues. The best way to prevent any holes or vulnerabilities is to find the weak spots and use secure patches to reinforce areas of concern.
According to Forrester’s State of Application Security Report, application vulnerabilities are the most common external attack method, making patch management critical to your company’s overall security. In fact, according to the Ponemon Institute, 57% of cyberattack victims report that their breaches could have been prevented by installing an available patch and even more chilling, 34% of those victims knew of the vulnerability, but hadn’t taken action.
Why? Perhaps it’s the sheer volume of vulnerabilities that arise each year.
Info Security Magazine reported that more than 18,000 Common Vulnerabilities and Exposures (CVEs) were published last year alone. That’s an average of around 50 CVEs a day! As technology continues to move more quickly, it’s expected so will potential vulnerabilities. With so many gaps in such a dynamic landscape, it can feel impossible to stay on top of making sure your applications are safe from attacks.
Beyond the sheer volume of constant new vulnerabilities, patching can be time consuming. A patch needs be tested first to make sure it 1. Works to eliminate the vulnerability and 2. Doesn’t adversely affect your installed software. In fact, 74% of companies say they simply can’t patch fast enough because the average time to patch is 102 days according to Ponemon.
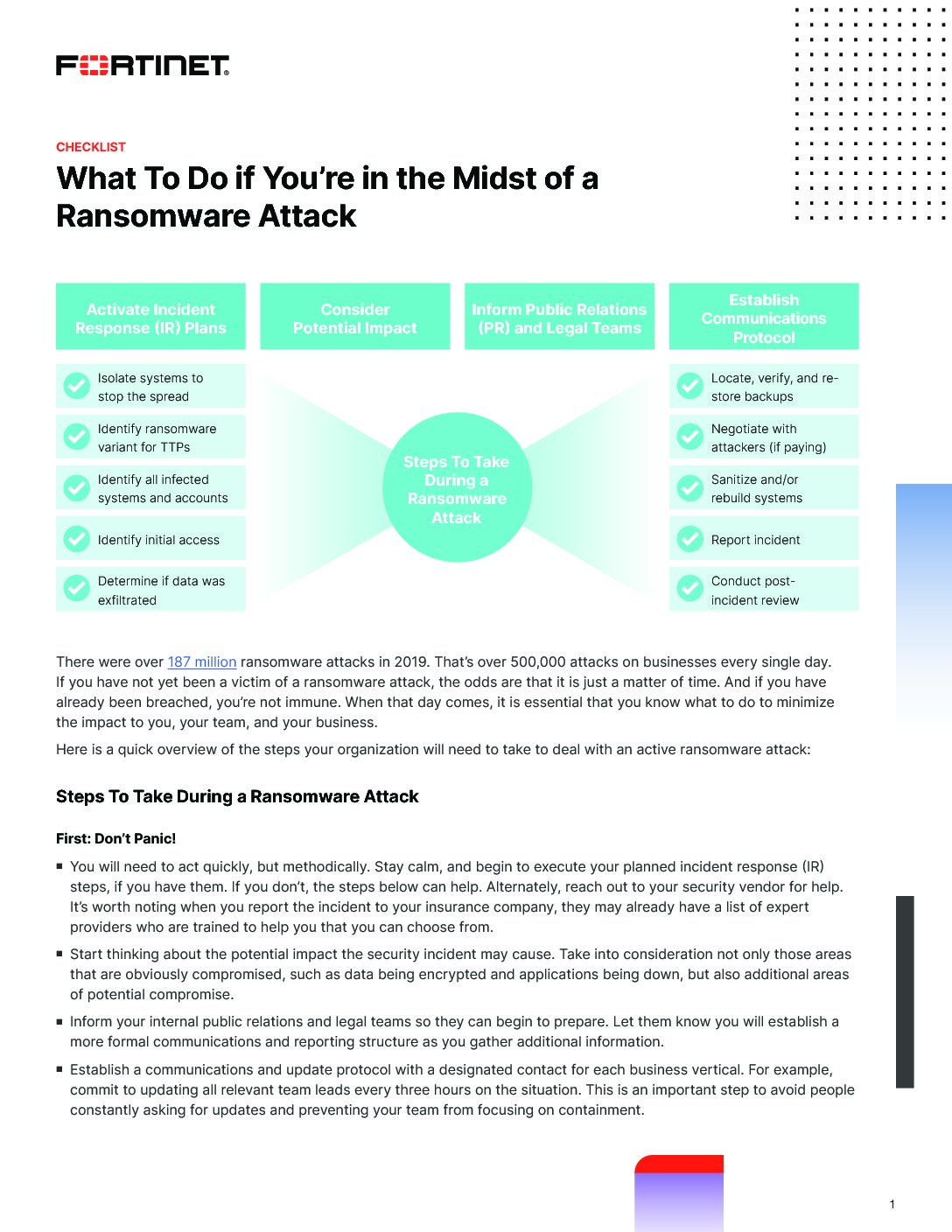
What To Do if You're in the Midst of a Ransomware Attack
We're seeing it everywhere, but don't panic just yet. Instead, download this free guide to learn the steps you can take to deal with an active ransomware attack.
How to Have an Effective Patch Management Process
Patching is important so you can ensure your company and customer data is secure against ransomware and other malware, which can take advantage of application vulnerabilities to hack your system.
So, what can you do to make sure you have an effective patch management process?
While patching may be time-consuming and difficult, it is a critical aspect to making sure your organization is safe and secure from cyberattacks. If you have concerns about increasing cyber threats and potential vulnerabilities in your applications, please reach out to our expert cybersecurity advisors. We can provide an assessment of your current patching process and see where there may be gaps before you become one of the 57% who experience a data breach due to poor patch management.
